Last Thursday, I was on a call with Greg — a threat intelligence analyst I've known since we both worked at the same SOC in 2019 — when he forwarded me a Palo Alto Unit 42 report with a one-word message: "Yikes."
That was underselling it.
A suspected Chinese state-backed cyber espionage operation, tracked as CL-STA-1087, has been quietly infiltrating Southeast Asian military organizations since at least 2020. Not weeks. Not months. Six years of patient, methodical intelligence collection, using custom-built malware that most detection tools would walk right past.
And the stuff they were looking for? Command and control structures. Joint exercises with Western armed forces. C4I systems. The kind of intelligence that doesn't just inform policy — it shapes how a country would fight a war.
The Discovery: A Suspicious PowerShell Script That Slept for Six Hours
Unit 42 researchers Lior Rochberger and Yoav Zemah stumbled onto the intrusion after detecting suspicious PowerShell execution on a military network. The script did something unusual: it entered a six-hour sleep state before doing anything.
Why? Because most automated sandbox environments give up after 5 to 10 minutes. Sleep for six hours, and the sandbox moves on. The malware wakes up in a real environment and creates reverse shells to a command-and-control server.
"That's not script kiddie stuff," Greg told me during our call, somewhere between his second and third Red Bull. "That's someone who has studied how defenders work and built countermeasures into their initial payload."
He's right. The exact initial access vector remains unknown — Unit 42 couldn't determine how the attackers got in — which, if you've ever done incident response, tells you something about the sophistication of the entry point itself.
AppleChris: The Backdoor That Uses Pastebin as a Dead Drop
The primary tool in the attackers' arsenal is a backdoor called AppleChris. And before you ask — no, it has nothing to do with Apple. The naming convention in threat research is about as logical as my filing system, which is to say, not at all.
Here's what makes AppleChris interesting:
The Dead Drop Resolver Pattern
Instead of hardcoding a C2 server address — which defenders can blocklist in about 30 seconds — AppleChris accesses a shared Pastebin account. The Pastebin paste contains a Base64-encoded address of the actual C2 server. Change the paste, change the C2. No malware update needed.
The Pastebin pastes date back to September 2020. That means this infrastructure has been operational for over five years.
Some versions of AppleChris also use Dropbox as a primary resolver, with Pastebin as fallback. Redundancy in malware infrastructure tells you something about the operator's risk calculus — they're planning for the long haul.
Capabilities
AppleChris can do essentially everything you'd want a remote access tool to do:
- Drive enumeration (what drives are connected?)
- Directory listing (what's in each folder?)
- File upload, download, and deletion
- Process enumeration (what software is running?)
- Remote shell execution (run any command)
- Silent process creation (run something without the user noticing)
The attackers deployed different versions across different endpoints after lateral movement. This is deliberate: if defenders find one variant and build a signature for it, the other variants survive. It's the malware equivalent of not putting all your eggs in one basket.
MemFun: The In-Memory Ghost
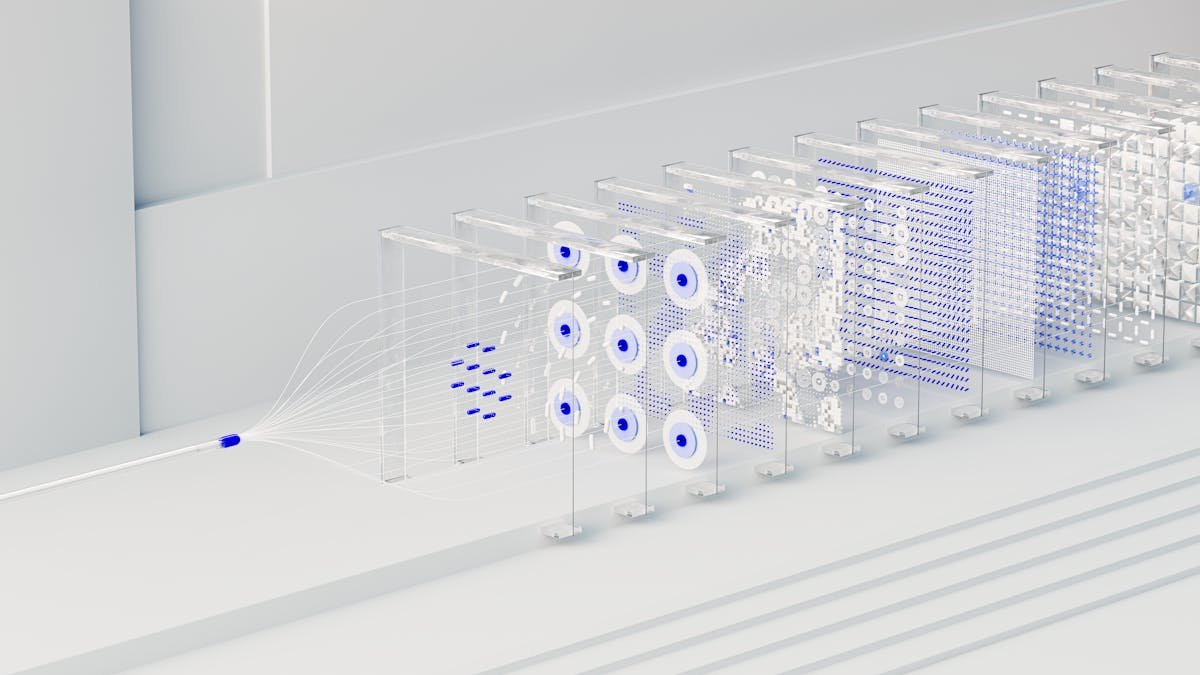
The second major tool, MemFun, takes things further. It uses a multi-stage chain that would make a Rube Goldberg machine jealous:
- An initial loader injects shellcode
- The shellcode launches an in-memory downloader
- The downloader fetches C2 config from Pastebin
- It contacts the C2 server
- The C2 server sends a DLL
- The DLL triggers the actual backdoor — entirely in memory
Since the backdoor DLL is fetched at runtime, it's never written to disk. Your endpoint detection tool that scans files? It'll never see MemFun. Your forensic analysis that images the hard drive? MemFun won't be there.
"The thing about in-memory malware," my friend Sandra explained — she does forensics for a $340M defense contractor — "is that it essentially disappears when you reboot. Which sounds good until you realize the loader is persistent and just downloads it again."
Sandbox Evasion
Both malware families employ sandbox evasion tactics at runtime:
- EXE variants: 30-second sleep timer before executing
- DLL variants: 120-second sleep timer before executing
These timers are specifically calibrated to outlast typical automated sandbox monitoring windows. Most sandboxes run samples for 60 to 90 seconds. A 120-second delay means the DLL does literally nothing while it's being watched, then activates after the sandbox has declared it clean.
What They Were Actually Looking For
This is the part that kept me up past 1 AM on a work night.
The attackers weren't stealing everything. They were surgically precise. Unit 42's report says they "actively searched for and collected highly specific files concerning":
- Military capabilities — what weapons systems, what quantities, what readiness levels
- Organizational structures — who reports to whom, what the command chain looks like
- Joint military activities — exercises with Western armed forces, particularly the US and allies
- C4I systems — Command, Control, Communications, Computers, and Intelligence infrastructure
- Official meeting records — what was discussed, what was decided, what was planned
This is textbook strategic intelligence collection. Not ransomware. Not cryptomining. Not data they can sell on the dark web. This is the kind of intelligence a nation-state collects when it's preparing for contingencies that involve those specific military organizations.
The Getpass Credential Harvester
Alongside AppleChris and MemFun, the attackers deployed a credential harvesting tool called Getpass. Not much detail in the report about its specifics, but the name and context suggest it targets Windows credentials — likely LSASS memory dumps or similar techniques.
Once you have credentials, you can move laterally. Once you move laterally, you can deploy more variants. Once you deploy more variants, you're entrenched. The cycle is self-reinforcing.
DLL Hijacking: The Entry Technique That Refuses to Die
AppleChris is launched via DLL hijacking (MITRE ATT&CK T1574.001). This technique exploits the way Windows loads dynamic-link libraries: if an attacker places a malicious DLL in a directory that gets searched before the legitimate one, the malicious DLL loads instead.
DLL hijacking has been around since the early 2000s. The fact that it's still effective in 2026 against military networks tells you something uncomfortable about the gap between attack sophistication and defense implementation.
What This Means for AI and Cybersecurity
Here's where this connects to what we cover at AICraftGuide.
The pattern Unit 42 describes — long-duration, low-noise, highly targeted espionage — is exactly the kind of threat that AI-powered security tools should catch. Behavioral anomalies. Unusual Pastebin lookups. PowerShell scripts that sleep for hours. DLL loads from unexpected paths.
But here's the uncomfortable truth: most AI security tools are trained on noisy attacks. Ransomware. Brute force. Phishing campaigns. The kind of threats that generate obvious signals. A state-backed APT that moves slowly, uses legitimate services (Pastebin, Dropbox), and sleeps through sandboxes? That's a different detection problem entirely.
Greg put it well: "We're building AI to catch bank robbers who run in screaming. These guys walk in wearing suits, sit down at a desk, and work there for six years."
The AI Arms Race in Espionage
The question isn't whether AI will be used in cyber espionage — it already is. The question is which side benefits more from the technology. Defenders get anomaly detection and automated response. Attackers get better evasion, more convincing social engineering, and the ability to process stolen intelligence faster.
CL-STA-1087 may not have used AI directly (the report doesn't say either way), but the operational discipline they demonstrated — different malware variants per endpoint, dead drop resolvers, multi-stage in-memory execution — is exactly the kind of tradecraft that AI could automate and scale.
What Organizations Should Do Right Now
If you work in defense, government, or any organization that handles sensitive geopolitical information:
- Audit your Pastebin and Dropbox network traffic. These are legitimate services, but if a system on your network is regularly checking Pastebin for specific pastes, that's worth investigating.
- Extend your sandbox dwell times. If your automated analysis runs for 60 seconds, some malware will outlast it. Consider 5-minute minimum analysis windows.
- Monitor for DLL hijacking indicators. Unexpected DLL loads from user-writable directories are a red flag.
- Implement memory forensics. Disk-based forensics won't catch MemFun. You need tools like Volatility or WinPmem that can capture and analyze RAM.
- Review PowerShell logging. Script Block Logging and Module Logging should be enabled and forwarded to a SIEM. A six-hour sleep command is trivially detectable if you're logging.
The Bigger Picture
Six years. Custom malware. Pastebin dead drops. In-memory execution. Surgical targeting of military intelligence. This is what patient, well-funded cyber espionage looks like in 2026.
And the scariest part isn't the malware. It's the question of how many similar campaigns are running right now that haven't been discovered yet.
I asked Greg that exact question. He paused longer than I was comfortable with.
"More than we think," he said. "Way more than we think."
The full Unit 42 report is available at unit42.paloaltonetworks.com. If you work in threat intelligence, it's required reading.
Related Reading
If you found this useful, check out these related articles: